3 Methods Create Better Adsense Profit Calculator With The help Of You…
페이지 정보

본문
 You need these links to be from good high quality websites and not created in a deceptive or spammy manner. And for example, SIDR npm bundle hasn't been maintained for six years but it surely has 500 day by day or weekly downloads still it's a highly regarded bundle so it is an excellent goal for impersonating as a result of in all probability somebody will not notice it as a result of it doesn't get updated, it has been the identical version for 6 years. The attacker creates new accounts, publishes new packages, primarily nonetheless focusing icons bundle. Yeah, so I downloaded one of many packages, which I analyzed. It also includes urls for other lookup columns, and then the response appears like this (only for one document!). It's like configuring your local mirror of npm repository, gain some insights and making certain that you're succesful to know what dependencies are getting used after which performing security analysis or those relies upon. What do we all know concerning the individuals or group behind IconBurst and what the target here is?
You need these links to be from good high quality websites and not created in a deceptive or spammy manner. And for example, SIDR npm bundle hasn't been maintained for six years but it surely has 500 day by day or weekly downloads still it's a highly regarded bundle so it is an excellent goal for impersonating as a result of in all probability somebody will not notice it as a result of it doesn't get updated, it has been the identical version for 6 years. The attacker creates new accounts, publishes new packages, primarily nonetheless focusing icons bundle. Yeah, so I downloaded one of many packages, which I analyzed. It also includes urls for other lookup columns, and then the response appears like this (only for one document!). It's like configuring your local mirror of npm repository, gain some insights and making certain that you're succesful to know what dependencies are getting used after which performing security analysis or those relies upon. What do we all know concerning the individuals or group behind IconBurst and what the target here is?
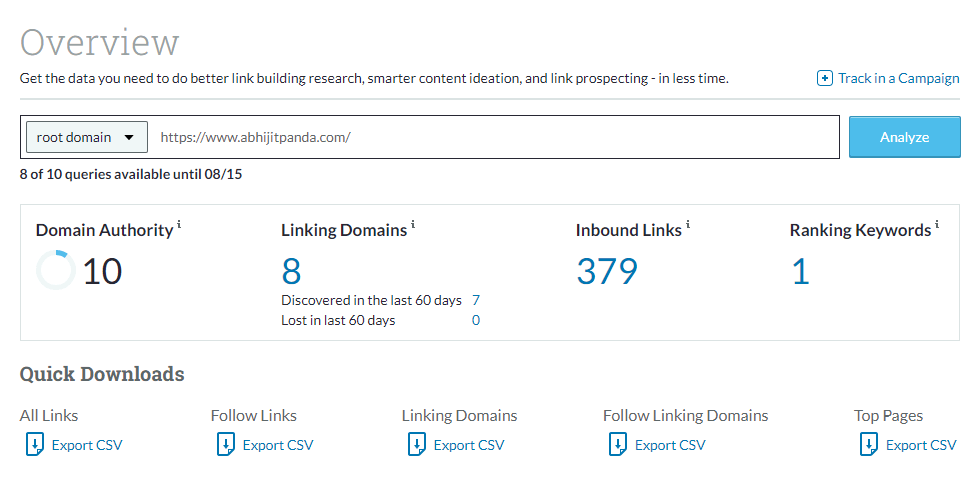 This IconBurst assault seems to be ongoing. And for website authority checker organizations, simply that this is a type of assault and a technique that adversaries are increasingly conscious of and using to their benefit. The sort of attack might be expected to be present for some extra time. So it is exhausting to detect it by automated analysis at the publishing time. What's vital is there isn't any simple means to stop somebody from publishing to npm as a result of it isn't arduous to change the content material of JavaScript file, particularly for those who perform obfuscation on it. These are being distributed on various channels and it is possible that a number of publishers are publishing to npm. What can be potential to do with your Javascript code is obfuscate it. But it is possible that different malicious actors have purchased these scripts from the original order. Because there are loads of modules that have submit-set up scripts and so they perform some motion instantly after you set up them. As we seen it last week, two new modules appeared so the tip customers should bear in mind of that menace.
This IconBurst assault seems to be ongoing. And for website authority checker organizations, simply that this is a type of assault and a technique that adversaries are increasingly conscious of and using to their benefit. The sort of attack might be expected to be present for some extra time. So it is exhausting to detect it by automated analysis at the publishing time. What's vital is there isn't any simple means to stop somebody from publishing to npm as a result of it isn't arduous to change the content material of JavaScript file, particularly for those who perform obfuscation on it. These are being distributed on various channels and it is possible that a number of publishers are publishing to npm. What can be potential to do with your Javascript code is obfuscate it. But it is possible that different malicious actors have purchased these scripts from the original order. Because there are loads of modules that have submit-set up scripts and so they perform some motion instantly after you set up them. As we seen it last week, two new modules appeared so the tip customers should bear in mind of that menace.
Support: The help folder accommodates two information: commands.js and index.js. Bear in mind reciprocal hyperlinks with a website might point out to Google the 2 sites are ‘related’ in some trend. Moz claims to have a brand new analysis tool known as Spam Score and it guarantees to assist webmasters clear their domains of unnatural hyperlinks. Dec 31, 2014New Tool: 'Inner Linking Profile'This new software crawls your website and analyzes your internal hyperlinks on autopilot. A wonderful technique to see which phrases may serve as LSI is through the use of Google AdWords’ Keyword Tool. You still want a method to maneuver guests along their journey once they land on your content material. The higher the Page Authority score of a web web page the more are the possibilities of specific net pages to rank in how a lot effort you need to place in order to improve this Page Authority score in search engine like Google. If you do not have any person like Karlo Zanki in your workforce, what do you do?
So if you bought questions on provide chain risk and attacks, use the chat feature and we are going to go this alongside to Karlo. Access log file is now using JSONL instead of custom format which is able to make working with logs simpler. Many obfuscators transfer strings and numbers into separate arrays after which entry them by index. It then analyzed the data set and helped me reach a conclusion that answered this particular query. For my part, they had been beginning with collecting PubG login credentials, which were also used to login on the pages and later switching to npm environment, JavaScript surroundings and broadening the attain, attempting to catch all type of login information moving on from simply PubG gameplay. Those are pages to observe. So it attacked all kinds of net pages wherever the module was used, accumulate in some cases usually searching for or all type tags in the html web page and submitting their content material, serializing it and submitting it to the type of controlled server. You can achieve this through the use of relevant key phrases in your content, optimizing meta tags and picture alt texts, and sustaining a clear and consumer-pleasant site construction.
If you loved this article and you would like to receive more info with regards to base64 to img please visit the web page.
- 이전글Everything You Will To Go Into Bar 25.02.16
- 다음글인하대역 푸르지오 에듀포레 라고 밝혔다. A 씨는 19일 오후 6시께 서울 25.02.16
댓글목록
등록된 댓글이 없습니다.


